Microsoft
With a wide-reaching ecosystem spanning productivity tools, cloud services, and operating systems, Microsoft caters to both enterprise and consumer markets. By incorporating Microsoft authentication into your product, you extend a streamlined login experience to users familiar with Microsoft's suite of services, enhancing accessibility and user trust.
How to setup the Microsoft auth provider
To enable Microsoft (opens in a new tab) as an auth provider, you will need to create a new App Registration from the Microsoft Azure Portal (opens in a new tab). Follow the official entra ID quickstart guide (opens in a new tab) for up to date instructions on how to do this.
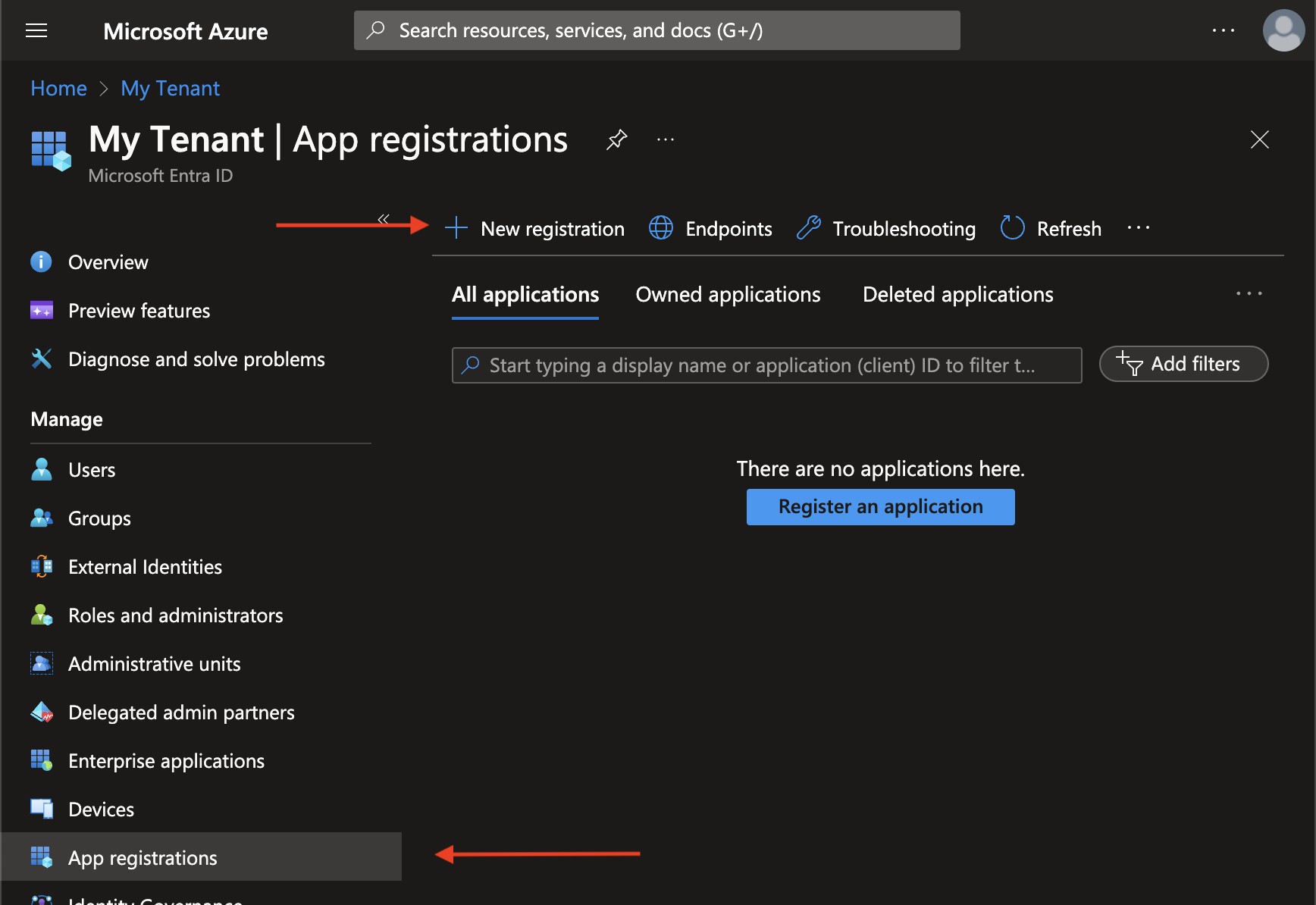
First, navigate to azure portal Entra ID then, App Registrations (opens in a new tab). From here you should click "New Registration".
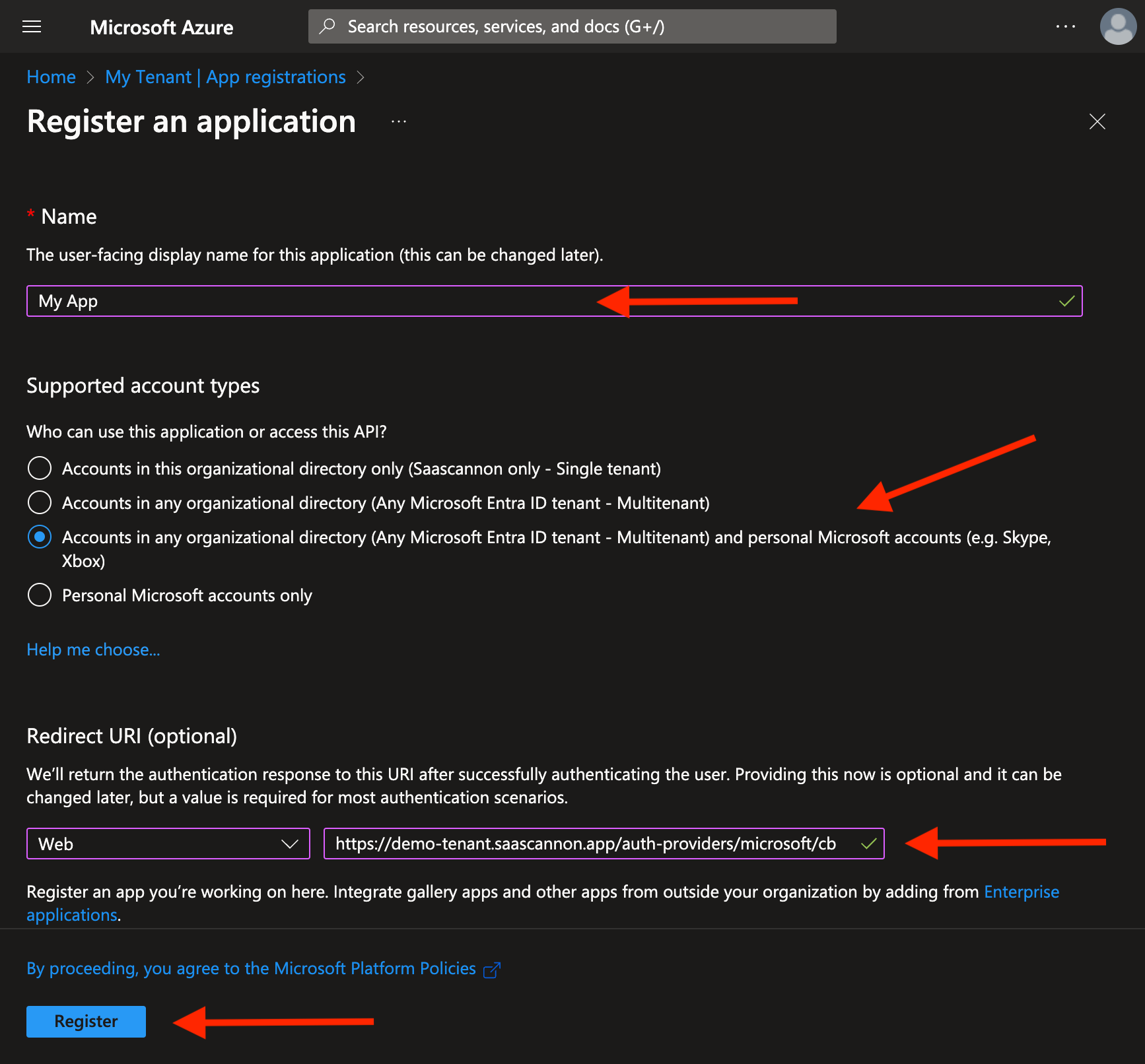
In the New Registration page, fill in your desired App Name, select supported account types, in most scenarios you will want "Accounts in any organizational directory (Any Microsoft Entra ID tenant - Multitenant) and personal Microsoft accounts (e.g. Skype, Xbox)", although this will depend on your use case. Then provide your microsoft redirect url and click "Register".
If you are unsure on how to find your callback URL in the Saascannon Dashboard (opens in a new tab), follow our guide on how to find your callback url for auth providers
Once your new app is registered, you will be presented with the details for your new app. From here, you will need to copy your app id and click to generate a new secret.
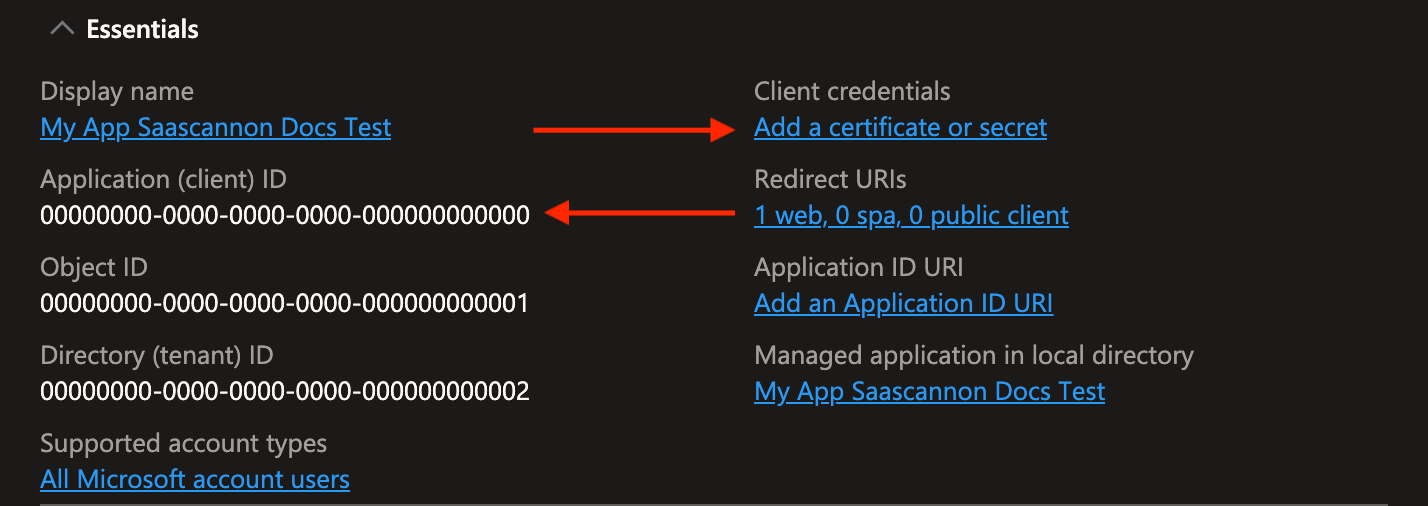
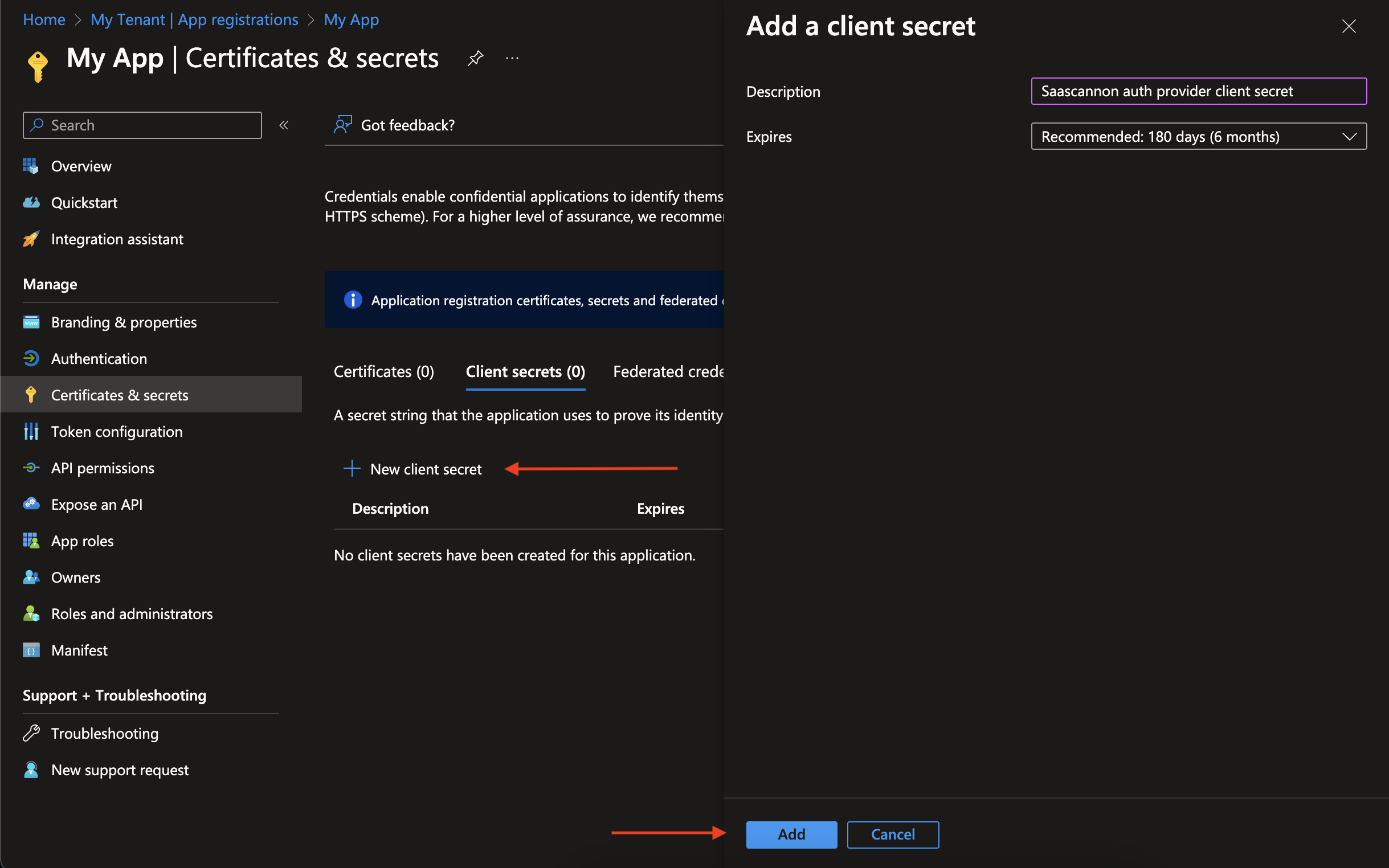
From the certificates and secrets page, click on "New client secret" to generate a new secret and provide a description and expiary.
Note that you will need to provide saascannon with the new secret when your generated one expires and you create a new one.
Once you have the app id and app secret, you can paste these into the "Enable Microsoft auth integration form" before clicking "Enable Microsoft Auth Integration".
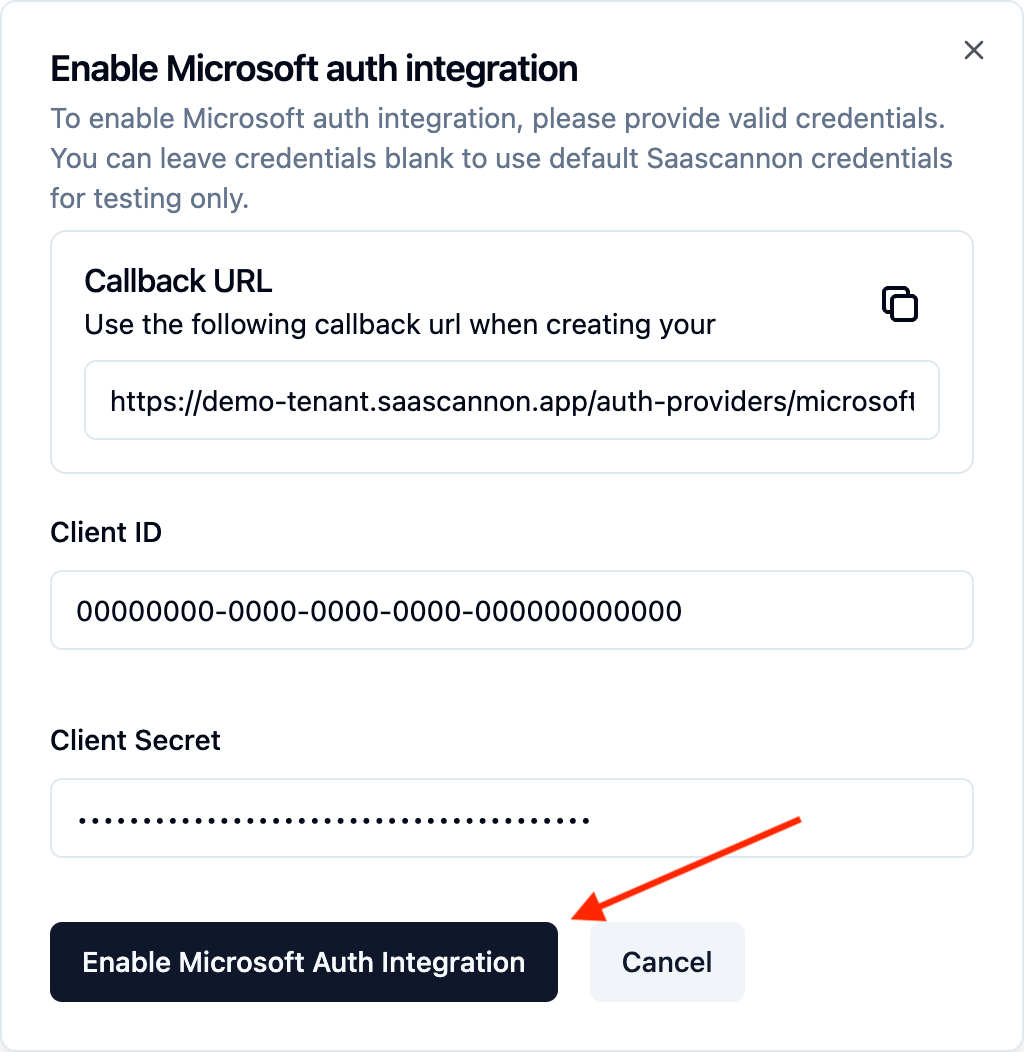
Congratulations! Users will now be able to login and link their accounts with Microsoft accounts in your saascannon tenant.